Opinion
Bitcoin Rollups – The Rock Or The Hard Place?
Published
3 months agoon
By
admin

Rollups have become the narrative focus of scaling Bitcoin lately, becoming the first thing to truly “steal the limelight” from the Lightning Network in terms of wider mindshare. Rollups aim to be an off-chain layer two that is not bound or constrained by the liquidity limitations that are central to the Lightning Network, i.e. end users required someone allocate (or “lend”) them funds ahead of time in order to be able to receive money, or intermediary routing nodes requiring channel balances that can facilitate the movement of the payment amount all the way from sender to receiver.
These systems were originally developed to function on Ethereum and other Turing complete systems, but as of late the focus has shifted to porting them to UTXO based blockchains such as Bitcoin. This article is not going to discuss the current state of things being implemented on Bitcoin currently, but going to discuss the function of an idealized rollup that people are aiming for in the long term depending on features Bitcoin currently does not support, namely the ability to verify Zero Knowledge Proofs (ZKPs) on Bitcoin directly.
The basic architecture of a roll is as follows: a single account (or in Bitcoin’s case UTXO), holds the balances of all users in the rollup. This UTXO contains a commitment in the form of a merkle root of a merkle tree that commits to all the current balances of existing accounts in the rollup. All of these accounts are authorized using public/private key pairs, so in order to propose an off-chain spend a user must still sign something with a key. This part of the structure allows users to leave without permission whenever they want, simply by crafting a transaction proving their account is part of the merkle tree, they can unilaterally exit the rollup without the operator’s permission.
The operator of the rollup must include a ZKP in transactions that update the merkle root of account balances on-chain in the process of finalizing off-chain transactions, without this ZKP the transaction will be invalid and therefore not includable in the blockchain. This proof allows people to verify that all changes to off-chain accounts were properly authorized by the account holder(s), and that the operator has not conducted a malicious update of balances to steal money from users or reallocate it to other users dishonestly.
The problem is, if only the root of the merkle tree is posted on-chain where users can view and access it, how do they get their branch in the tree in order to be capable of exiting without permission when they want to?
Proper Rollups
In a proper rollup, the information is put directly into the blockchain everytime that new off-chain transactions are confirmed and the state of the rollup accounts change. Not the entire tree, that would be absurd, but the information necessary to reconstruct the tree. In a naive implementation, the summary of all existing accounts in the rollup would have balances and accounts simply added in the transaction updating the rollup.
In more advanced implementations, a balance diff is used. This is essentially a summary of what accounts have had money added to or subtracted from them during the course of an update. This allows each rollup update to only include the changes to account balances that occur. Users can then simply scan the chain and “do the math” from the beginning of the rollup to arrive at the current state of account balances, which allows them to reconstruct the merkle tree of current balances.
This saves a lot of overhead and blockspace (and therefore money) while still allowing users to guarantee access to the information needed for them to exit unilaterally. Including this data in a formal rollup that uses the blockchain to make it available to users is mandated by the rules of the rollup, i.e. a transaction that does not include the account summary or account diff is considered an invalid transaction.
Validiums
The other way to handle the problem of data availability for users to withdraw is to put the data somewhere else besides the blockchain. This introduces subtle issues, the rollup still needs to enforce that the data was made available somewhere else. Traditionally other blockchains are used for this purpose, specifically designed to function as data availability layers for systems like rollups.
This creates the dilemma of security guarantees being as strong. When the data is posted directly to the Bitcoin blockchain, consensus rules can guarantee it is correct with absolute certainty. However when it is posted to an external system, the best it can do is verify an SPV proof that the data was posted to another system.
This entails verifying an attestation that data exists on other chains, which is ultimately an oracle problem. Bitcoin’s blockchain cannot verify anything completely except what occurs on its own blockchain, the best it can do is verify a ZKP. A ZKP however cannot verify that a block containing rollup data was actually publicly broadcast after being produced. It cannot verify that external information is actually publicly available to everyone.
This opens the door to data withholding attacks, where a commitment to the data being published is created and used to advance the rollup, but the data is not actually made available. This renders users funds beyond their ability to withdraw. The only real solution to this is to depend entirely on the value and incentive structure of systems completely external to Bitcoin.
The Rock and Hard Place
This creates a dilemma in terms of rollups. When it comes to the data availability issue, there is essentially a binary choice between posting the data to the Bitcoin blockchain or somewhere else. This choice has massive implications for both rollup security and sovereignty, as well as their scalability.
On one hand, using the Bitcoin blockchain for the data availability layer introduces a hard ceiling on how much rollups can scale. There is only so much blockspace, and that puts an upper limit on how many rollups can exist at one time and how many transactions all rollups in aggregate can process off-chain. Every rollup update requires blockspace proportional to the amount of accounts that have had balance changes since the last update. Information theory only allows data to be compressed so much, and at that point there is no more potential for scaling gains.
On the other hand, using a different layer for data availability removes the hard ceiling on scalability gains, but it also introduces new security and sovereignty issues. In a rollup using Bitcoin for data availability it is literally not possible for the state of the rollup to change without the data needed by users to withdraw being atomically posted to the blockchain. With Validiums, that guarantee depends entirely on the ability of whatever external system is being used to resist gaming and data withholding.
Any block producer on the external data availability system is now capable of holding Bitcoin rollup users’ funds hostage by producing a block and not actually broadcasting it to make the data available.
So which will it be, if we ever do get to an ideal rollup implementation on Bitcoin that actually enables unilateral user withdrawal? The rock, or the hard place?
Source link
You may like


BTC Risks Falling To $20K If This Happens

Most Layer 2 solutions are still struggling with scalability


Here’s why Stellar Price Could Go Parabolic Soon
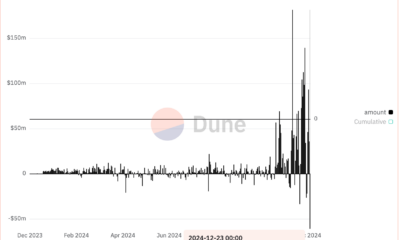

Perp-Focused HyperLiquid Experiences Record $60M in USDC Net Outflows


Experts say these 3 altcoins will rally 3,000% soon, and XRP isn’t one of them


Robert Kiyosaki Hints At Economic Depression Ahead, What It Means For BTC?
Blockchain
Most Layer 2 solutions are still struggling with scalability
Published
2 hours agoon
December 23, 2024By
admin
Disclosure: The views and opinions expressed here belong solely to the author and do not represent the views and opinions of crypto.news’ editorial.
Since pivoting to a layer 2-centric approach, the Ethereum (ETH) ecosystem has relied heavily on L2 solutions to scale. However, these solutions are struggling to compete effectively, especially under pressure from alternatives like Solana (SOL). During the recent meme coin craze, Solana attracted much of the activity due to its advantages: low fees, high transaction speed, and user-friendliness.
To understand the challenges, it’s essential to examine why L2 solutions have not demonstrated the scalability and cost advantages that were widely anticipated.
Why meme projects favor Solana over Ethereum L2s
Meme projects have significantly contributed to the recent surge in market activity. These projects favor Solana for several reasons beyond user-friendliness:
- Low fees: Solana’s low transaction costs make it ideal for fee-sensitive applications like memecoins.
- High speed: Solana’s multithreaded architecture enables high throughput, ensuring seamless user experiences.
- Better developer experience: Solana’s tools and ecosystem are optimized for ease of use, attracting developers and projects.
Why is scalability important?
Scalability is fundamentally measured by the number of transactions a blockchain can process. A highly scalable blockchain can handle more TXs while offering lower fees, making it crucial for widespread adoption and maintaining a seamless user experience.
This is especially important for grassroots projects like meme coins, many of which are short-lived and highly fee-sensitive. Without scalability, these projects cannot thrive, and users will migrate to platforms that offer better efficiency and cost-effectiveness.
Why Ethereum L2s aren’t up to the challenge
Architectural limitations of Ethereum. Ethereum has long faced scalability issues, and L2 rollups are its primary solution to these problems. L2s operate as independent blockchains that process transactions off-chain while posting transaction results and proofs back to Ethereum’s mainnet. They inherit Ethereum’s security, making them a promising scaling approach.
However, Ethereum’s original design poses inherent challenges. Ethereum’s founder, Vitalik Buterin, has admitted that “Ethereum was never designed for scalability.” One of the key limitations is the lack of multithreading in the Ethereum Virtual Machine. The EVM, which processes transactions, is strictly single-threaded, meaning it can handle only one transaction at a time. In contrast, Solana’s multithreaded architecture allows it to process multiple transactions simultaneously, significantly increasing throughput.
L2s inheriting Ethereum’s limitations. Virtually all L2 solutions inherit Ethereum’s single-threaded EVM design, which results in low efficiency. For instance, Arbitrum: With a targeted gas limit of 7 million per second and each coin transfer costing 21,000 gas, Arbitrum can handle about 333 simple transactions per second. More complex smart contract calls consume even more gas, significantly reducing capacity. Optimism: With a gas limit of 5 million per block and a block time of 2 seconds, Optimism can handle only about 119 simple transfers per second. Gas-intensive operations further reduce this capacity.
Unstable fees. Another major issue with Ethereum and its L2 solutions is unstable fees during periods of high network activity. For applications relying on low and stable fees, this is a critical drawback. Projects like meme coins are especially fee-sensitive, making Ethereum-based L2s less attractive.
Lack of interoperability between L2s. The scalability argument for having multiple L2s only holds if contracts on different L2s can interact freely. However, rollups are essentially independent blockchains, and accessing data from one rollup to another is as challenging as cross-chain communication. This lack of interoperability significantly limits the potential of L2 scalability.
What can L2s do to further scale?
Embed features to enhance interoperability. Ethereum L1 needs to do more to support interoperability among L2s. For example, the recent ERC-7786: Cross-Chain Messaging Gateway is a step in the right direction. While it doesn’t fully resolve the interoperability issue, it simplifies communication between L2s and L1, laying the groundwork for further improvements.
Architectural updates: Diverge from the existing L1 design. To compete with multithreaded blockchains like Solana, L2s must break free from Ethereum’s single-threaded EVM design and adopt parallel execution. This may require a complete overhaul of the EVM, but the potential scalability gains make it a worthwhile endeavor.
Future milestones
Ethereum’s L2 solutions face significant challenges in delivering the scalability and cost-effectiveness that applications like meme coins demand. To stay competitive, the ecosystem must address fundamental architectural limitations, enhance interoperability, and embrace innovations in blockchain design. Only by doing so can Ethereum L2s achieve the scalability needed to support widespread adoption and fend off competition from emerging blockchains like Solana.

Laurent Zhang
Laurent Zhang is the president and founder of Arcology Network, a revolutionizing Ethereum layer-2 solution with the first-ever EVM-equivalent, multithreaded rollup—offering unparalleled performance and efficiency for developers building the next generation of decentralized applications. With an executive leadership and innovation background, Laurent holds a degree from Oxford Brookes University. Laurent’s professional journey includes over a decade of experience in science, research, engineering, and leadership roles. After graduating in 2005, he joined MKS Instruments as an Algorithm Engineer. From 2010 to 2012, he worked as a research engineer at the Alberta Machine Intelligence Institute, followed by a position as a research scientist at Baker Hughes from 2012 to 2014. He then served as vice president of engineering at Quikflo Health between 2016 and 2018. Since 2017, Laurent has been the president of Arcology Network, being a visionary of a future where blockchain technology reaches its full potential, offering unmatched scalability, efficiency, and innovation.
Source link


Recently, BlackRock released an educational video explaining Bitcoin, which I thought was great—it’s amazing to see Bitcoin being discussed on such a massive platform. But, of course, Bitcoin X (Twitter) had a meltdown over one specific line in the video: “There is no guarantee that Bitcoin’s 21 million supply cap will not be changed.”
HealthRnager from Natural News claimed, “Bitcoin has become far too centralized, and now the wrong people largely control its algorithms. They are TELLING you in advance what they plan to do.”
Now, let me be clear: this is total nonsense. The controversy is overhyped, and the idea that BlackRock would—or even could—change bitcoin’s supply is laughable. The statement in their video is technically true, but it’s just a legal disclaimer. It doesn’t mean BlackRock is plotting to inflate bitcoin’s supply. And even if they were, they don’t have the power to pull it off.
Bitcoin’s 21 million cap is fundamental—it’s not up for debate. The entire Bitcoin ecosystem—miners, developers, and nodes—operates on this core principle. Without it, Bitcoin wouldn’t be Bitcoin. And while BlackRock is a financial giant and holds over 500,000 Bitcoin for its ETF, its influence over Bitcoin is practically nonexistent.
Bitcoin is a proof-of-work (PoW) system, not a proof-of-stake (PoS) system. It doesn’t matter how much bitcoin BlackRock owns; economic nodes hold the real power.
Let’s play devil’s advocate for a second. Say BlackRock tries to propose a protocol change to increase bitcoin’s supply. What happens? The vast network of nodes would simply reject it. Bitcoin’s history proves this. Remember Roger Ver and the Bitcoin Cash fork? He had significant influence and holdings, yet his version of bitcoin became irrelevant because the majority of economic actors didn’t follow him.
If Bitcoin could be controlled by a single entity like BlackRock, it would’ve failed a long time ago. The U.S. government, with its endless money printer, could easily acquire 10% of the supply if that’s all it took to control Bitcoin. But that’s not how Bitcoin works. Its decentralized nature ensures no single entity—no matter how powerful—can dictate its terms.
So, stop worrying about BlackRock “changing” Bitcoin. Their influence has hard limits. Even if they tried to push developers to change the protocol, nodes would reject it. Bitcoin’s decentralization is its greatest strength, and no one—not BlackRock, not Michael Saylor—can change that.
This article is a Take. Opinions expressed are entirely the author’s and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.
Source link
Opinion
It’s Time to Admit It – There Are Only 2.1 Quadrillion Bitcoins
Published
2 days agoon
December 21, 2024By
admin
If the above statement offends you, you might not have read the Bitcoin source code.

https://x.com/pete_rizzo_/
Of course, I’m sure you’ve heard that there are 21 million bitcoin – and this is true, the Bitcoin protocol allows for only “21 million bitcoin” to be created, yet these larger denominations can be subdivided into 100 million sub-units each.
Call them whatever you want, there are only 2.1 quadrillion monetary units in the protocol.
This dollars and cents differential has long been the subject of debate – in the time of Satoshi, Bitcoin’s creator, the dual conventions, Bitcoin having both a bulk denomination, and a smaller unit, was not much of a concern. There were questions about whether the software would work at all, and bitcoin were so worthless, selling them in bulk was the only rational option.
Rehashing this debate is BIP 21Q, a proposal to the Bitcoin users authored by John Carvalho, founder of Synonym, creator of the Pubky social media platform, and a tenured contributor whose work dates back to the days of the influential Bitcoin-assets collective.
In short, the BIP proposes that network actors – the various wallets and exchanges – change how Bitcoin denominations are displayed, with the smallest unit of the protocol renamed “bitcoins,” as opposed to “satoshis,” as they have been commonly called.
Here are the specifics of the BIP:
Redefinition of the Unit:
- Internally, the smallest indivisible unit remains unchanged.
- Historically, 1 BTC = 100,000,000 base units. Under this proposal, “1 bitcoin” equals that smallest unit.
- What was previously referred to as “1 BTC” now corresponds to 100 million bitcoins under the new definition.
Terminology:
- The informal terms “satoshi” or “sat” are deprecated.
- All references, interfaces, and documentation SHOULD refer to the base integer unit simply as “bitcoin.”
Display and Formatting:
- Applications SHOULD present values as whole integers without decimals.
- Example:
- Old display: 0.00010000 BTC
- New display: 10000 BTC (or ₿10000)
Unsurprisingly, the debate around the BIP has been hostile. For one, it’s not a technical BIP, though this is not a requirement of the BIP process. Suffice to say, it’s perhaps the most general BIP that has been proposed under the BIP process to date, as it mainly deals with market conventions and user onboarding logic, not any changes to the software rules.
However, I have to say, I find the proposal compelling. Nik Hoffman, our News Editor, does not, preferring to stick to the market affirmative.
Yet, I think the proposal raises relevant questions: why should new users be forced to compute their Bitcoin balances using only decimals? Surely this has the adverse side effect of making commerce difficult – it’s simply antithetical to how people think and act today.
Also, in terms of savings, at an $100,000 BTC price, it isn’t exactly compelling to think you could be spending a whole year earning 1 BTC, though that may be.
Indeed, there have been various debates for all kinds of units – mBTC, uBTC – that play around with the dollars and cents convention, but Carvalho here is wisely skipping to the end, preferring just to rip the band-aid off. $1 would buy 1,000 bitcoins under his proposal.
What’s to like here, and I argued this during a Lugano debate on the topic in 2023, is that it keeps both the larger BTC denomination and the smaller unit, now bitcoins. They are both important, and serve different functions.
My argument then was that having a larger denomination like BTC (100 million bitcoins) is important. If there was no “BTC unit,” the press and financial media would be faced to reckon that “1 bitcoin” is still worth less than 1 cent.
How much mainstream coverage and interest do we think there would be? I’d bet not very much.
In this way, BIP 21Q is a best-of-both-worlds approach.
The financial world, press, and media can continue championing the meteoric rise in value of “BTC,” while everyday users can get rid of decimals and complex calculations, trading the only real Bitcoin unit guaranteed to exist in perpetuity.
This article is a Take. Opinions expressed are entirely the author’s and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.
Source link

BTC Risks Falling To $20K If This Happens

Most Layer 2 solutions are still struggling with scalability

Here’s why Stellar Price Could Go Parabolic Soon

Perp-Focused HyperLiquid Experiences Record $60M in USDC Net Outflows

Experts say these 3 altcoins will rally 3,000% soon, and XRP isn’t one of them

Robert Kiyosaki Hints At Economic Depression Ahead, What It Means For BTC?

BNB Steadies Above Support: Will Bullish Momentum Return?

Metaplanet makes largest Bitcoin bet, acquires nearly 620 BTC

Tron’s Justin Sun Offloads 50% ETH Holdings, Ethereum Price Crash Imminent?

Investors bet on this $0.0013 token destined to leave Cardano and Shiba Inu behind

End of Altcoin Season? Glassnode Co-Founders Warn Alts in Danger of Lagging Behind After Last Week’s Correction

Can Pi Network Price Triple Before 2024 Ends?

XRP’s $5, $10 goals are trending, but this altcoin with 7,400% potential takes the spotlight

CryptoQuant Hails Binance Reserve Amid High Leverage Trading

Trump Picks Bo Hines to Lead Presidential Crypto Council
182267361726451435

Why Did Trump Change His Mind on Bitcoin?

Top Crypto News Headlines of The Week

New U.S. president must bring clarity to crypto regulation, analyst says

Will XRP Price Defend $0.5 Support If SEC Decides to Appeal?

Bitcoin Open-Source Development Takes The Stage In Nashville

Ethereum, Solana touch key levels as Bitcoin spikes

Bitcoin 20% Surge In 3 Weeks Teases Record-Breaking Potential

Ethereum Crash A Buying Opportunity? This Whale Thinks So

Shiba Inu Price Slips 4% as 3500% Burn Rate Surge Fails to Halt Correction

Washington financial watchdog warns of scam involving fake crypto ‘professors’

‘Hamster Kombat’ Airdrop Delayed as Pre-Market Trading for Telegram Game Expands

Citigroup Executive Steps Down To Explore Crypto
Mostbet Güvenilir Mi – Casino Bonus 2024

NoOnes Bitcoin Philosophy: Everyone Eats
Trending
 3 months ago
3 months ago182267361726451435
 Donald Trump5 months ago
Donald Trump5 months agoWhy Did Trump Change His Mind on Bitcoin?

 24/7 Cryptocurrency News4 months ago
24/7 Cryptocurrency News4 months agoTop Crypto News Headlines of The Week
 News4 months ago
News4 months agoNew U.S. president must bring clarity to crypto regulation, analyst says

 Price analysis4 months ago
Price analysis4 months agoWill XRP Price Defend $0.5 Support If SEC Decides to Appeal?

 Opinion5 months ago
Opinion5 months agoBitcoin Open-Source Development Takes The Stage In Nashville

 Bitcoin5 months ago
Bitcoin5 months agoEthereum, Solana touch key levels as Bitcoin spikes

 Bitcoin5 months ago
Bitcoin5 months agoBitcoin 20% Surge In 3 Weeks Teases Record-Breaking Potential